Access Control and Role Management
Design intelligent access controls that balance security with productivity across SAP and integrated systems.

Secure & streamlined access for SAP environments
Effective Access Control & Role Management is vital for safeguarding critical ERP environments, especially SAP ERP systems. We deliver robust solutions to define, enforce and monitor role based access controls, ensuring compliance, minimizing risk, and safeguarding sensitive data. Our services include comprehensive SAP GRC implementations, segregation-of-duties (SoD) analyses, role design optimization and continuous access monitoring, enabling precise, compliant and secure user permissions that align seamlessly with your organizational needs
What we offer
Effective role design is critical to minimize risk while maximizing productivity. Our SAP role design and redesign services follow the principle of least privilege, aligning access precisely with business functions and compliance requirements. Leveraging best practices and advanced analytics, we streamline SAP ERP roles, enhancing security, reducing complexity and supporting audit readiness while empowering users to operate efficiently within clearly defined boundaries.
Role design that secures SAP, empowers users, and optimizes business fficiency.
Segregation of Duties (SoD) conflicts can expose SAP environments to fraud and non-compliance. Our comprehensive SAP SoD analysis systematically identifies, assesses and resolves conflicting roles. By employing proactive strategies and automated solutions, we help clients maintain compliance, simplify audits and significantly reduce internal risk, preserving the integrity and transparency of critical business processes
with intelligent conflict matrices, compensating controls and process redesign.
Sensitive access requires vigilant oversight to prevent unauthorized activities in SAP systems. Our Sensitive Access Review and Monitoring services provide continuous insight and rigorous tracking of high-risk user activities. Utilizing SAP GRC tools and real-time analytics, we detect anomalies rapidly, enforce security policies and deliver proactive responses, ensuring sensitive information remains protected and compliance standards consistently upheld.
SAP sensitive access enhanced security, trusted compliance.
Periodic user access reviews are critical but often tedious. Our automated SAP User Access Review & Certification solutions simplify this process, delivering streamlined, accurate evaluations of user permissions. By automating workflows and providing clear documentation, we enhance compliance reporting accuracy, reduce manual efforts, improve audit readiness and significantly decrease compliance risks across your SAP ERP environment.
SAP user access reviews for reliable, audit ready compliance.
Privileged access in SAP ERP carries heightened risks and demands robust management. Our Privileged Access Management (PAM) services deliver targeted oversight, access restriction and accountability for SAP power users. Leveraging advanced monitoring tools and enforced just-in-time access, we significantly reduce misuse potential, enhance compliance capabilities and maintain rigorous control, safeguarding your most critical SAP systems from threats and unauthorized actions.
emergency access with just-in-time elevation and session recording.
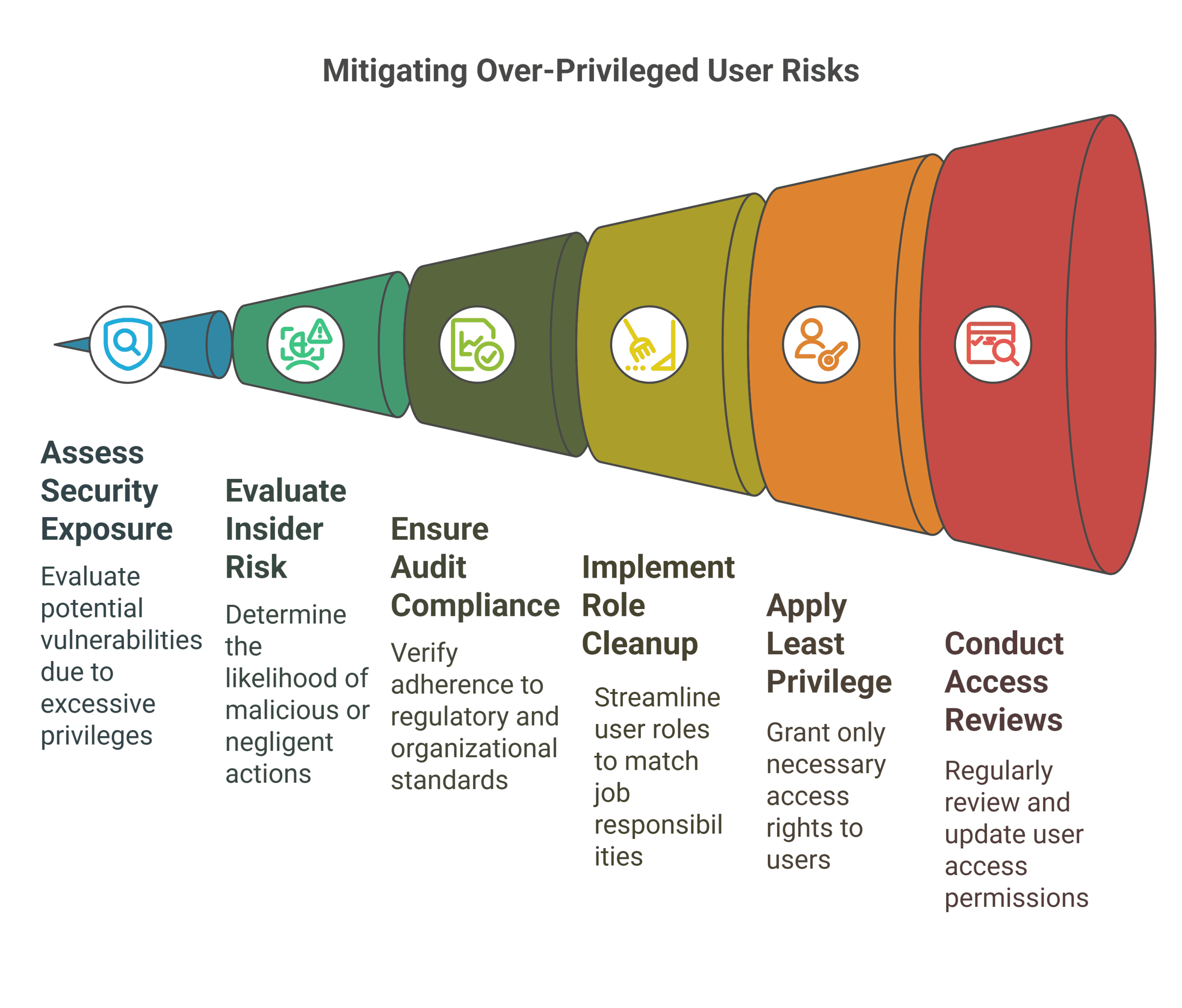
The hidden security gap undermining resilience
Excessive access rights, role drift, and weak oversight create hidden security gaps and audit risks. Strengthens your Zero Trust posture with automated access reviews, role clarity and least privilege enforcement. Our proactive approach includes ongoing recertification and monitoring to prevent privilege creep, reduce internal threats and ensure continuous compliance across hybrid and cloud environments..
What is on your mind about Access Control & Role Management ?
Get in Touch ?
Helping clients is at the core of what we do
Please fill out the simple form and submit your question here. We will respond as quickly as possible
Related Services

We transform SAP security from reactive to strategic, delivering tailored advisory that identifies vulnerabilities, optimizes controls and aligns cybersecurity with business objectives. Our approach combines SAP certified expertise,...

We transform access management into a strategic advantage, implementing intelligent IAG frameworks that balance security, compliance and productivity across SAP ecosystems. Our approach combines AI-driven role mining, just-in-time...

ERP systems are prime targets for cyberattacks. We identify weaknesses before attackers do. We simulate real-world breaches, assess SAP role-based access risks and harden configurations. Protect your ERP...

Leveraging automated detection, rapid response protocols, and predictive analytics, we identify and mitigate risks swiftly, minimizing operational disruptions, protecting critical data and ensuring your ERP landscape remains resilient,...

We transform GRC from a cost center to a strategic enabler, implementing intelligent controls that protect SAP systems while accelerating business processes. Our SAP-certified approach combines AI-driven risk...



