ERP Vulnerability and Penetration Testing
Protect your ERP from data theft, fraud and downtime with tested cybersecurity strategies.

Secure your ERP before hackers exploit It
ERP systems, particularly SAP, often hold your organization’s most sensitive data, making them prime targets for cyberattacks. Our comprehensive ERP vulnerability and penetration testing identifies hidden risks within your SAP environment. By simulating real-world attacks, including unauthorized access attempts, we proactively expose and remediate weaknesses, ensuring robust security defenses, regulatory compliance and business continuity. Partner with us to fortify your ERP landscape and safeguard critical operations against sophisticated cyber threats
What we offer
Business-critical applications like SAP ERP often attract targeted cyber threats. Our Application Penetration Testing service rigorously assesses your SAP landscape, identifying vulnerabilities, security gaps and potential exploits. Leveraging advanced penetration techniques and industry best practices, we simulate sophisticated attacks to proactively detect weaknesses before they are exploited, helping you reinforce application security, maintain compliance and safeguard sensitive business data from breaches.
Strengthening and protecting your SAP applications from hidden vulnerabilities.
Misconfigured ERP systems, such as SAP, Oracle or Dynamics, are susceptible to cyber threats and operational risks. Our ERP Configuration Security Reviews methodically assess your ERP setup against best practices and industry benchmarks. By identifying configuration gaps, authorization weaknesses and security misalignments, we provide tailored recommendations to strengthen your ERP environment, ensuring maximum protection, regulatory compliance and operational reliability.
Ensure secure ERP configurations to minimize risks.
SAP systems require secure data transmission and up-to-date defenses. Our SAP Transport Layer Security and Patch Management services comprehensively evaluate and harden your SAP landscape, applying timely critical patches. We safeguard your SAP environment against data interception, unauthorized access, and emerging vulnerabilities, reducing cyber risk, enhancing system resilience and ensuring compliance.
unpatched ERP systems are low hanging fruit for attackers. Encrypt, patch and protect.
Our SAP Platform Hardening services strengthen your SAP Basis environment, systematically eliminating vulnerabilities. Leveraging proven methodologies, we implement rigorous security controls, optimize system parameters and fortify infrastructure components. This strategic approach ensures your SAP landscape stays secure, resilient and aligned with industry leading security frameworks, protecting core business operations and safeguarding sensitive data.
leave your business exposed. Fortify your SAP foundation, security starts at the core.
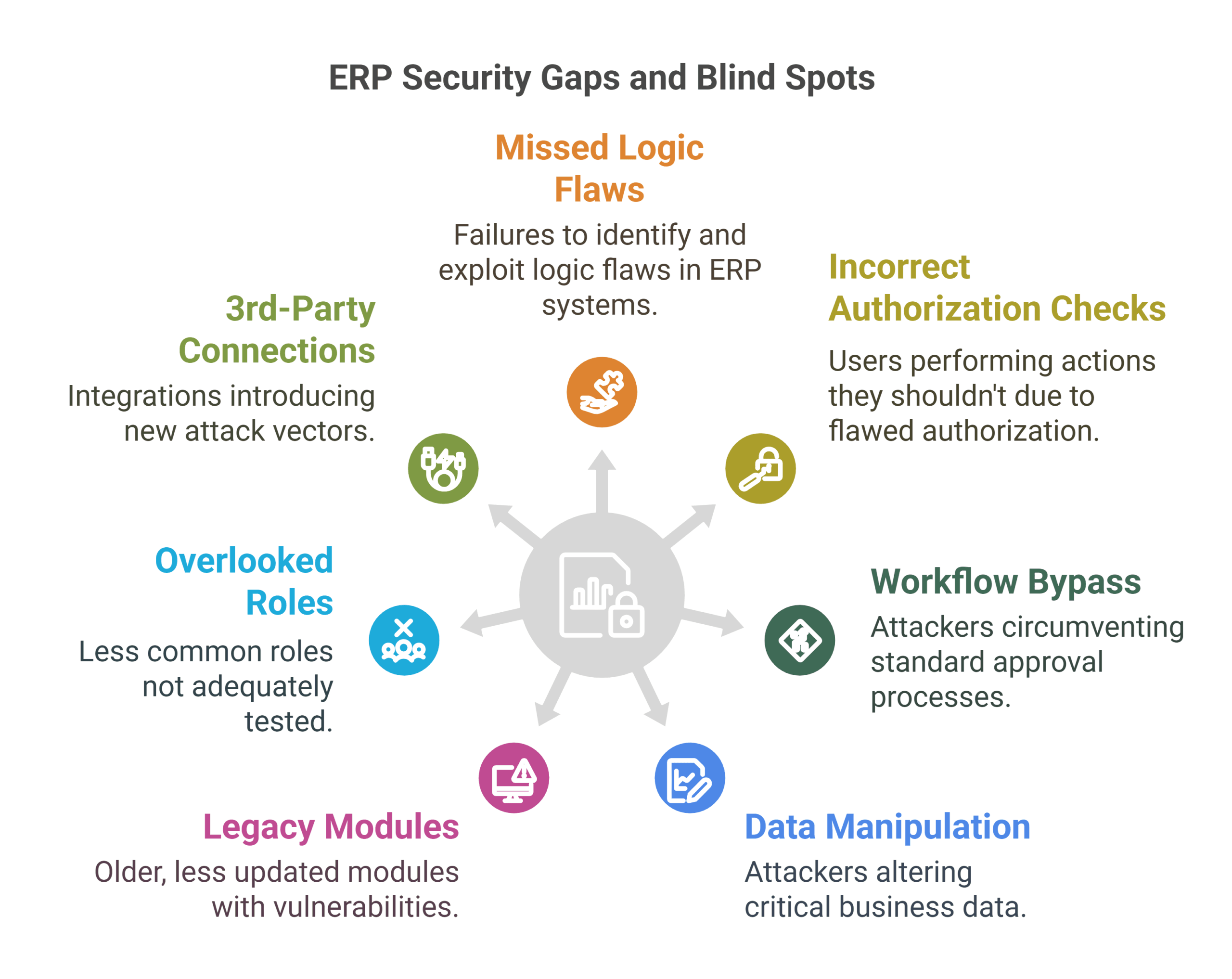
Real risk reduction in ERP environments
ERP systems are deeply complex and many penetration tests fail to detect business logic vulnerabilities. Unscanned workflows, misconfigured roles, and integration gaps invite costly breaches. We goes beyond surface level testing, identifying hidden weaknesses in permissions, logic, and access controls. We uncover ERP blind spots before attackers do, protecting your operations from disruption, data loss and multi million dollar breach consequences.
What is on your mind about ERP Vulnerability & Penetration Testing ?












Get in Touch ?
Helping clients is at the core of what we do
Please fill out the simple form and submit your question here. We will respond as quickly as possible
Related Services

We transform SAP security from reactive to strategic, delivering tailored advisory that identifies vulnerabilities, optimizes controls and aligns cybersecurity with business objectives. Our approach combines SAP certified expertise,...

We transform access management into a strategic advantage, implementing intelligent IAG frameworks that balance security, compliance and productivity across SAP ecosystems. Our approach combines AI-driven role mining, just-in-time...

Leveraging automated detection, rapid response protocols, and predictive analytics, we identify and mitigate risks swiftly, minimizing operational disruptions, protecting critical data and ensuring your ERP landscape remains resilient,...

We transform GRC from a cost center to a strategic enabler, implementing intelligent controls that protect SAP systems while accelerating business processes. Our SAP-certified approach combines AI-driven risk...

We design intelligent access controls that balance security with productivity, implementing SAP GRC-certified role models, just-in-time provisioning, and AI-driven anomaly detection. Our approach minimizes insider threats while ensuring...
