Identity and Access Governance
Transform access management into a strategic advantage, implementing intelligent IAG frameworks

Secure every SAP interaction, govern every access
What we offer
Effective management of user identities across SAP environments is crucial for security and productivity. Our Centralized Identity Lifecycle Management services streamline identity provisioning, role management and user offboarding within SAP ERP, minimizing compliance risks and operational delays. By integrating robust identity governance frameworks, we protect your systems from unauthorized access and potential vulnerabilities identified through proactive application penetration testing.
lifecycle, from onboarding to role changes to offboarding across SAP and integrated systems.
Enhance SAP ERP security and usability through streamlined Single Sign-On (SSO) and robust Multi-Factor Authentication (MFA). Our tailored implementation simplifies access, reduces password fatigue, and strengthens defenses against credential-related threats, significantly reducing cyber risks across your SAP environment.
adaptive MFA, balancing user experience with robust authentication across Fiori, GUI and mobile access points.
Precisely manage access within SAP ERP using robust RBAC and ABAC frameworks. We tailor these frameworks to align closely with your organizational needs and compliance mandates, dynamically adjusting access rights to minimize security risks, ensuring regulatory adherence and maintaining operational efficiency.
where access adjusts based on department, location, risk level and other real-time attributes.
Seamlessly integrate your SAP ERP with leading identity providers like Okta and Azure AD. Our integration services deliver secure, frictionless access management, enhance identity governance, reduce administrative burdens and provide comprehensive visibility and control over user access across hybrid and cloud environments.
identity platforms to SAP enabling centralized governance without compromising SAP’s native security model.
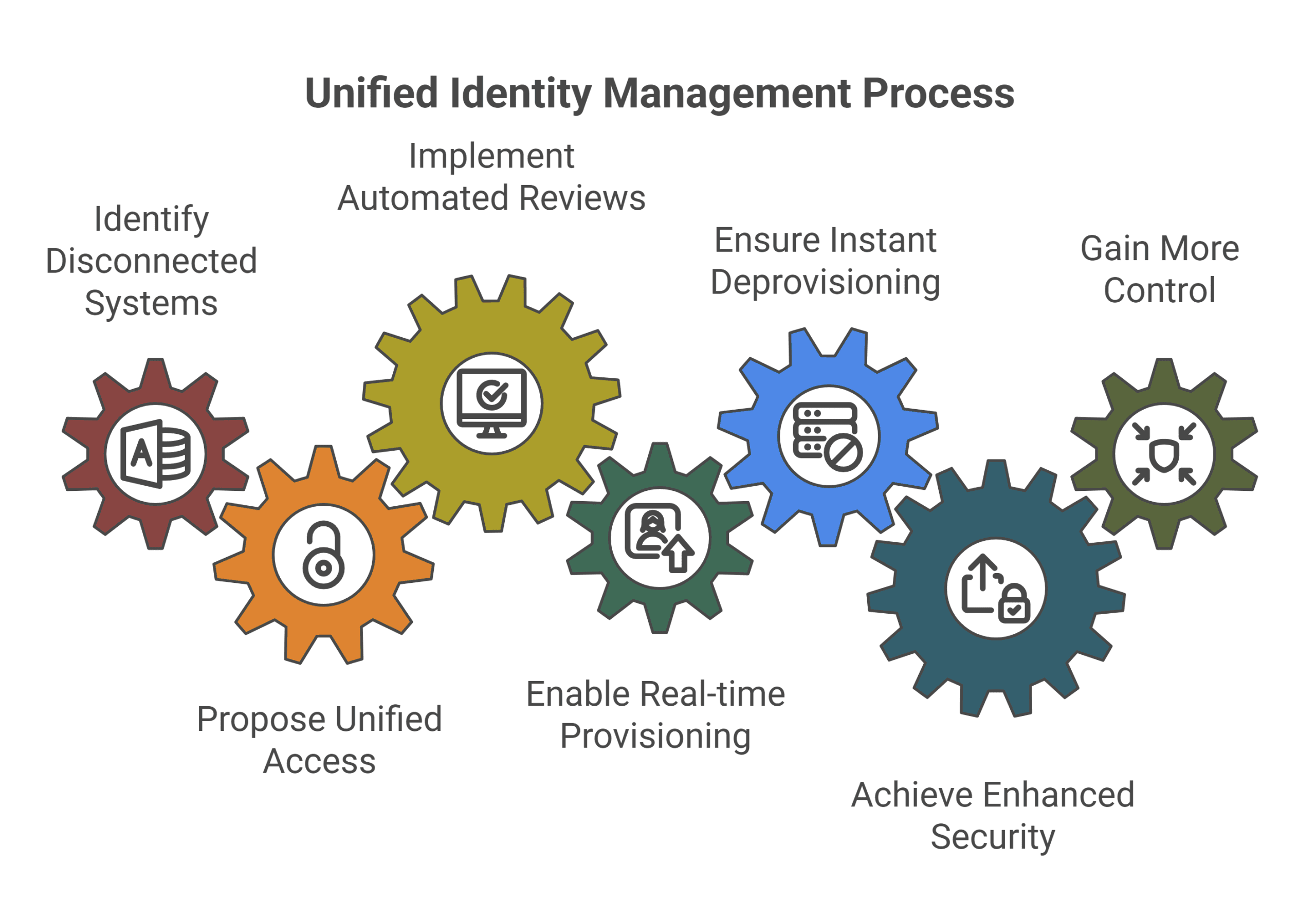
The case for unified access governance
Fragmented access systems lead to compliance gaps and unmanaged risk. Leverage our services to unify identity and access governance across cloud and on-premise environments, ensuring consistent control and visibility. With real-time lifecycle automation, we manage provisioning and immediate revocation from hire to exit, reducing insider threats, ensuring audit readiness and protecting sensitive data at every stage of the identity journey.
What is on your mind about Identity & Access Governance ?












Get in Touch ?
Helping clients is at the core of what we do
Please fill out the simple form and submit your question here. We will respond as quickly as possible
Related Services

We transform SAP security from reactive to strategic, delivering tailored advisory that identifies vulnerabilities, optimizes controls and aligns cybersecurity with business objectives. Our approach combines SAP certified expertise,...

ERP systems are prime targets for cyberattacks. We identify weaknesses before attackers do. We simulate real-world breaches, assess SAP role-based access risks and harden configurations. Protect your ERP...

Leveraging automated detection, rapid response protocols, and predictive analytics, we identify and mitigate risks swiftly, minimizing operational disruptions, protecting critical data and ensuring your ERP landscape remains resilient,...

We transform GRC from a cost center to a strategic enabler, implementing intelligent controls that protect SAP systems while accelerating business processes. Our SAP-certified approach combines AI-driven risk...

We design intelligent access controls that balance security with productivity, implementing SAP GRC-certified role models, just-in-time provisioning, and AI-driven anomaly detection. Our approach minimizes insider threats while ensuring...
