Penetration Testing
Secure your applications and protect data. Proactive penetration testing for ultimate defense

Detect and fix weaknesses now
Mitigate cyber threats with our Penetration Testing and Red Teaming services. We simulate real-world attacks to uncover hidden vulnerabilities beyond patchable flaws. These include weak credentials, misconfigurations, exposed data, and ineffective policies. By combining expert analysis with advanced tools, we help strengthen your defenses, identify blind spots and enhance your overall security posture.
What we offer
Our Application Penetration Testing services are designed to uncover and eliminate vulnerabilities before they can be exploited. Using advanced tools and expert methodologies, we simulate real-world attacks to assess the security, reliability, and resilience of your applications. Each engagement is customized to your environment and risk profile, ensuring targeted results.
we help you protect sensitive data, maintain compliance, and build user trust in an ever-evolving threat landscape.
As cloud adoption grows, securing your environment is more important than ever. Our Cloud Penetration Testing services simulate real-world attacks to identify vulnerabilities across your cloud infrastructure, covering networks, applications, storage, and user configurations. We detect risks such as exposed storage, insecure APIs, and misconfigured permissions to help prevent breaches and ensure compliance.
Our expert driven assessments provide actionable insights to strengthen your cloud security posture, safeguard sensitive data, and align with industry regulations. Stay ahead of threats and protect your cloud environment with proactive, comprehensive security testing tailored to your organization’s needs.
Cloud technology is a key business enabler, lets help keep your business safe
Network Penetration Testing evaluates internal and external infrastructures to uncover vulnerabilities and strengthen defenses. Internal testing simulates insider threats across LANs and internal systems, while external testing targets public facing assets like websites and email servers. By proactively addressing vulnerabilities, we help protect sensitive data, ensure compliance, and support business continuity. These tests are a vital part of a strong cybersecurity strategy, keeping your organization secure against evolving cyber threats from both inside and outside the network.
tools and methodologies to identify and mitigate risks.
Our Ransomware Attack Simulation services help organizations proactively prepare for one of the most critical cybersecurity threats today. By simulating real world ransomware scenarios, we assess your systems’ resilience, identify vulnerabilities, and evaluate your incident response capabilities. Our experts mimic advanced ransomware tactics, such as encryption, lateral movement, and data exfiltration, to uncover weaknesses in your defenses. Protect your business from costly disruptions, data loss, and reputational damage by staying ahead of evolving ransomware threats.
we empower your team to strengthen detection, prevention, and recovery strategies.
Attackers frequently mimic trusted sources or fabricate urgent situations to manipulate individuals into compromising security. Our Social Engineering Testing services simulate real-world attacks like phishing, baiting and pretexting to identify gaps in employee security awareness. We assess responses to threats, knowledge of protocols, and incident reporting capabilities. Post-assessment, we provide a detailed report with vulnerabilities, actionable recommendations, and strategies to mitigate risks. By investing in these services, organizations can strengthen their cybersecurity posture.
critical assets against evolving social engineering threats. Contact us to learn how we can help secure your organization.
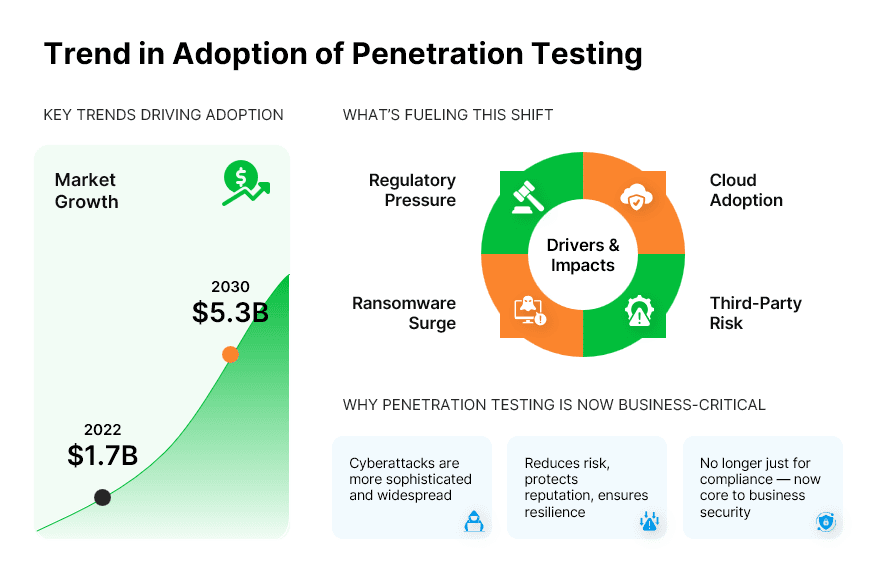
Trend in adoption of Penetration Testing
The rise of ransomware, cloud adoption, and remote work has expanded attack surfaces, making penetration testing essential. It helps organizations proactively identify vulnerabilities, meet compliance requirements, and validate Zero Trust models. Integrated into DevSecOps, continuous testing enhances security across CI CD pipelines. With Red and Purple Teaming for improved response and AI driven tools for greater efficiency, penetration testing is key to staying ahead of evolving cyber threats.
What is on your mind about Penetration Testing ?








Get in Touch ?
Helping clients is at the core of what we do
Please fill out the simple form and submit your question here. We will respond as quickly as possible
Related Services

Our expert threat hunters blend advanced security intelligence with human analysis to detect unusual activities, uncover potential risks, and provide swift incident responses. This proactive strategy reduces the...

Managing vulnerabilities can be complex and time-intensive, especially for organizations with growing security demands. Our comprehensive Vulnerability Management (VM) services help alleviate this challenge by identifying and addressing...

With our team of skilled security professionals, you gain proactive defense mechanisms, minimizing potential breaches before they cause harm. Outsourcing this critical function allows your business to focus...

We provide around the clock Managed Security Services to safeguard your business from cyber threats. Our expert Managed Security Operation Center (SOC) team monitors your networks. Leverage our...
Many organizations are unprepared to manage network security incidents. Our Managed Digital Forensics and Incident Response (DFIR) services help identify and address incidents, conduct forensic investigations, and uncover...

