Security Advisory and Optimization
Transform SAP security from reactive to strategic optimizing controls and aligning cybersecurity with business goals.

Advisory & optimization for SAP centric enterprises
Enhancing SAP cybersecurity is not just about protection, it is a strategic resilience. Our Security Advisory & Optimization service delivers expert assessments, tailored security roadmaps and targeted improvements specifically designed for SAP ERP environments. Leveraging best practices and proactive vulnerability management, we transform cybersecurity into a strategic enabler, reducing risk and optimizing your security posture to protect your critical data and streamline compliance with evolving regulations.
What we offer
In today's threat landscape, protecting your SAP ERP environment demands strategic foresight. Our Cybersecurity Strategy & Roadmap services deliver actionable, prioritized plans aligning your security posture with business goals. By identifying vulnerabilities, optimizing controls, and guiding proactive investments, we help you build a robust SAP ERP cybersecurity framework, ensuring compliance, reducing risk exposure, and safeguarding your most critical assets against evolving cyber threats.
roadmaps aligning threat prevention, innovation, evolving SAP architecture & regulatory compliance.
We design tailored security policies and procedures specifically for your SAP environment, aligning best practices with regulatory compliance and business objectives. Our methodical approach ensures practical, enforceable policies that embed security into daily operations, providing clarity for users, streamlining compliance efforts and establishing a consistent security culture across your organization.
Clear & comprehensive ERP security policies are critical for managing risks effectively.
Our comprehensive SAP Security Health Check evaluates your system's current cybersecurity posture, identifying gaps, assessing maturity levels, and recommending enhancements. Using structured frameworks and benchmarks, we pinpoint improvement opportunities, optimize security controls and help you achieve superior protection, compliance and operational resilience in your SAP ERP environment.
maturity assessments are essential to maintain robust ERP security.
Our specialized ERP Security Awareness Training programs educate your SAP users on recognizing threats, understanding responsibilities, and adopting best practices. Through interactive and engaging training sessions, we foster a security-conscious culture, significantly reducing risks associated with phishing, unauthorized access, and misuse, and ensuring your ERP environment remains secure at all operational levels.
of cybersecurity breaches. Empower your team & strengthen your security.
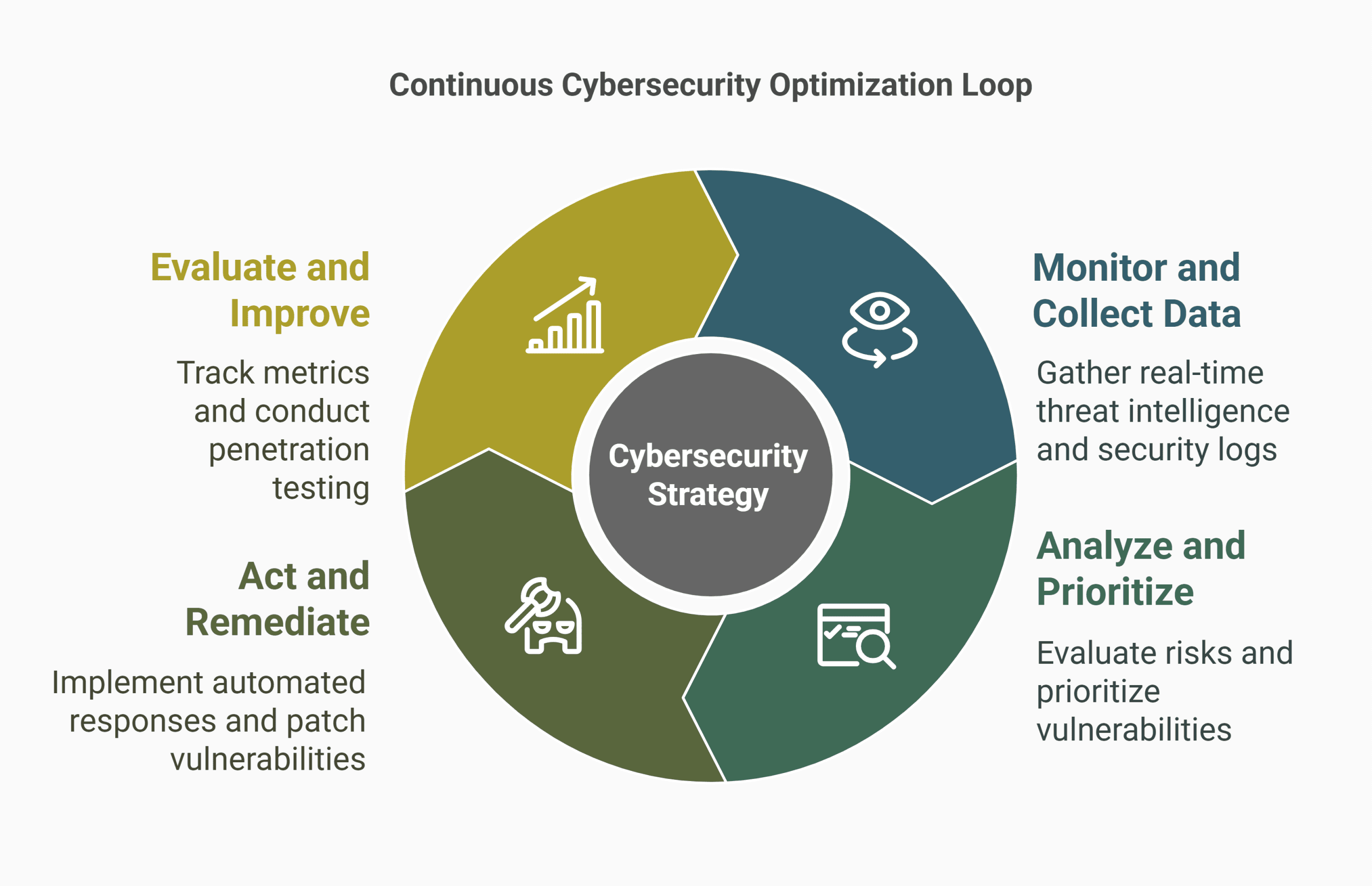
Discover what is missing in most cyber strategies
Many cybersecurity strategies fail because they are static, built once, rarely reassessed and blind to evolving risks. This leads to outdated controls, wasted investments and poor incident response. We address the gap with a continuous optimization loop, assessing security posture, tuning controls, and aligning defenses to real world threats. Our expert led advisory ensures your cybersecurity strategy adapts, improves and delivers measurable resilience.
What is on your mind about Security Advisory & Optimization ?




Get in Touch ?
Helping clients is at the core of what we do
Please fill out the simple form and submit your question here. We will respond as quickly as possible
Related Services

We transform access management into a strategic advantage, implementing intelligent IAG frameworks that balance security, compliance and productivity across SAP ecosystems. Our approach combines AI-driven role mining, just-in-time...

ERP systems are prime targets for cyberattacks. We identify weaknesses before attackers do. We simulate real-world breaches, assess SAP role-based access risks and harden configurations. Protect your ERP...

Leveraging automated detection, rapid response protocols, and predictive analytics, we identify and mitigate risks swiftly, minimizing operational disruptions, protecting critical data and ensuring your ERP landscape remains resilient,...

We transform GRC from a cost center to a strategic enabler, implementing intelligent controls that protect SAP systems while accelerating business processes. Our SAP-certified approach combines AI-driven risk...

We design intelligent access controls that balance security with productivity, implementing SAP GRC-certified role models, just-in-time provisioning, and AI-driven anomaly detection. Our approach minimizes insider threats while ensuring...


