Security Monitoring and Threat Detection
Proactive Security. Rapid Detection. Protected SAP Environments

Proactive monitoring for resilient enterprises
Robust security monitoring and proactive threat detection are critical in safeguarding your SAP ERP environment against evolving cyber threats. We implement continuous, real-time surveillance using advanced security analytics and SAP specific threat intelligence. Leveraging automated detection, rapid response protocols, and predictive analytics, we identify and mitigate risks swiftly, minimizing operational disruptions, protecting critical data and ensuring your ERP landscape remains resilient, secure and compliant.
What we offer
In complex ERP environments like SAP, proactive log monitoring and alerting are essential to detect security threats swiftly. Our ERP log monitoring services leverage advanced Security Information and Event Management (SIEM) and native SAP security tools to deliver real-time visibility into your ERP environment. With customizable alerting and actionable intelligence, we swiftly identify, investigate and respond to suspicious activities, securing your SAP systems against unauthorized access and ensuring compliance readiness.
SIEM to detect fraud, data leaks and unauthorized changes.
Our real-time threat detection service monitors SAP ERP landscapes continuously, quickly identifying threats and vulnerabilities using intelligent threat indicators and advanced detection algorithms. By integrating real-time intelligence with automated responses, we ensure swift resolution and protect your critical ERP assets against sophisticated cyber threats, preserving business continuity, data integrity and regulatory compliance.
SAP environments using behavioral analytics and SAP certified threat signatures.
Traditional security measures alone cannot counter evolving ERP threats. We employ machine learning to understand normal user and system activities within SAP ERP. We detect deviations instantly, revealing hidden threats like insider risks and unauthorized access attempts. With sophisticated anomaly detection, your organization gains predictive insights, enabling proactive mitigation and safeguarding sensitive ERP data against complex cyber threats.
We baseline normal SAP activities per role, then flag anomalies. Predict, detect & protect.
Integrating your SAP ERP systems with Security Operations Center (SOC) tools enhances threat visibility and accelerates response times. Our integration services seamlessly connect SAP ERP security data with leading SOC and monitoring platforms, enabling unified, end-to-end threat management. Leveraging automation, intelligent alerts and consolidated dashboards, we streamline threat detection and response, strengthening ERP cybersecurity while simplifying management and regulatory compliance across your enterprise environment.
your existing SIEM, enabling SOC teams to investigate ERP threats alongside IT alerts without SAP expertise.
Are you detecting what matters?
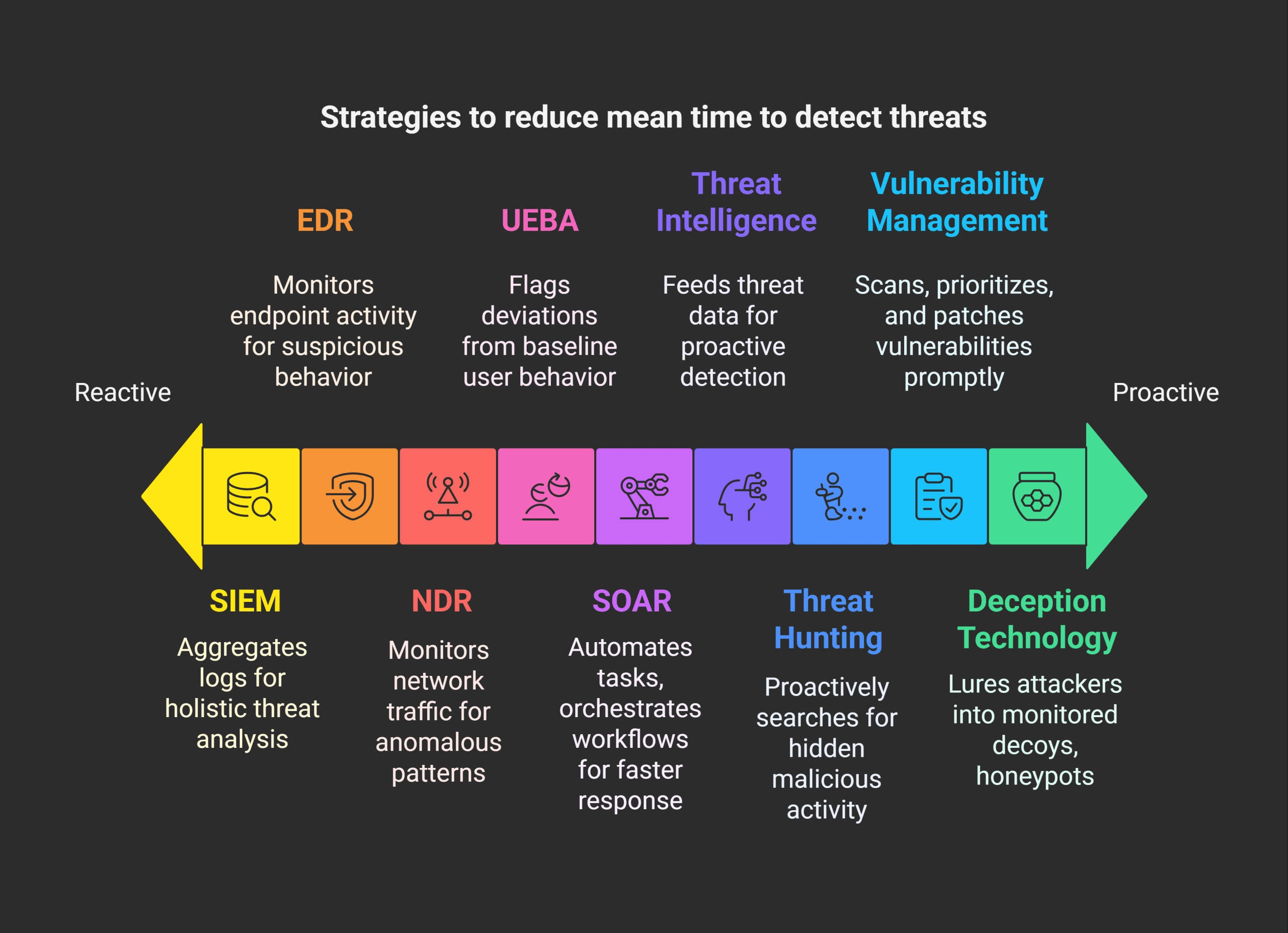
Slow detection and alert fatigue put your business at serious risk. We reduces Mean Time to Detect (MTTD) through intelligent correlation, automation and expert driven analysis. Filter out noise, prioritize real threats and stop breaches before they escalate. Unlike legacy SOCs, our AI-powered threat prediction and integrated response capabilities deliver proactive, continuous defense improving visibility, reducing downtime and strengthening your overall cybersecurity posture.
What is on your mind about Security Monitoring & Threat Detection ?








Get in Touch ?
Helping clients is at the core of what we do
Please fill out the simple form and submit your question here. We will respond as quickly as possible
Related Services

We transform SAP security from reactive to strategic, delivering tailored advisory that identifies vulnerabilities, optimizes controls and aligns cybersecurity with business objectives. Our approach combines SAP certified expertise,...

We transform access management into a strategic advantage, implementing intelligent IAG frameworks that balance security, compliance and productivity across SAP ecosystems. Our approach combines AI-driven role mining, just-in-time...

ERP systems are prime targets for cyberattacks. We identify weaknesses before attackers do. We simulate real-world breaches, assess SAP role-based access risks and harden configurations. Protect your ERP...

We transform GRC from a cost center to a strategic enabler, implementing intelligent controls that protect SAP systems while accelerating business processes. Our SAP-certified approach combines AI-driven risk...

We design intelligent access controls that balance security with productivity, implementing SAP GRC-certified role models, just-in-time provisioning, and AI-driven anomaly detection. Our approach minimizes insider threats while ensuring...

